Authorization List
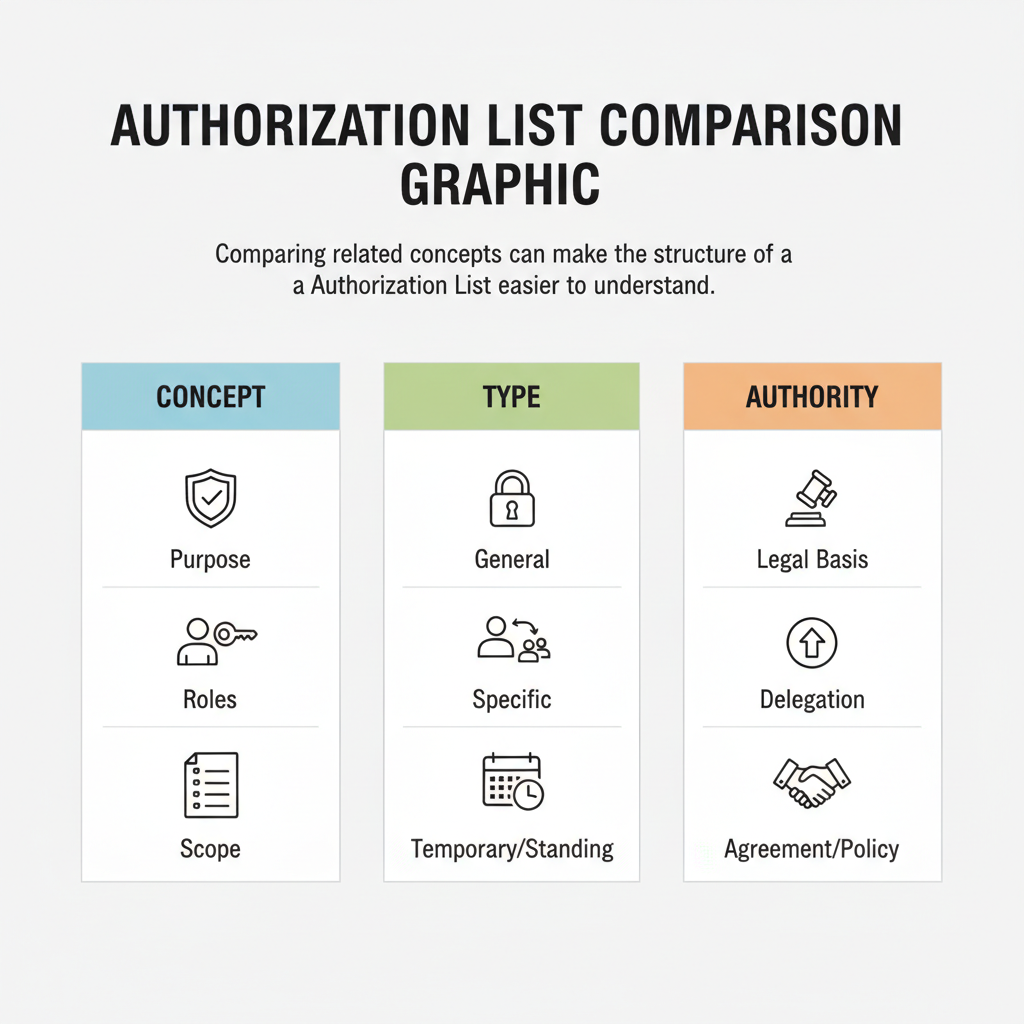
An Authorization List is a formal record or structured system that delineates approved permissions for specific actions, services, or access within an organization.
Authorization Scope Type
Select the main area for which you are granting authorizations. You can specify details for each authorized party later.
Table of Contents
What is an Authorization List?
An Authorization List is a structured record or system detailing approved permissions for specific actions, services, or access. It serves as a critical component in various sectors, from healthcare to information technology, ensuring that only authorized entities receive particular benefits or access. The primary purpose of such a list is to control and verify eligibility, prevent unauthorized activities, and streamline processes while maintaining compliance with established regulations.
Purpose and Scope
The fundamental purpose of an authorization list is to establish a clear framework for permission management. It acts as a reference point to confirm that a request aligns with pre-approved criteria or conditions. This systematic approach helps to mitigate risks, reduce improper payments, and ensure that resources are allocated appropriately according to defined policies and legal mandates.
The scope of authorization lists varies significantly depending on the context in which they are employed. In some instances, they detail specific medical services or equipment that require prior approval, while in others, they outline security standards for cloud products used by government agencies. Regardless of the application, these lists are integral to maintaining operational integrity and accountability within complex systems.
Applications in Healthcare
In the healthcare sector, authorization lists are extensively used to manage patient care and financial transactions, particularly within federal programs like Medicare and Medicaid. These lists are crucial for ensuring that medical items and services are medically necessary and appropriately billed.
- Prior Authorization for Medical Services - Health plans and providers utilize authorization processes to approve medical items and services before they are rendered (CMS.gov). This includes procedures, medications, and durable medical equipment.
- Electronic Prior Authorization (ePA) - The Centers for Medicare & Medicaid Services (CMS) is actively working to streamline this process through electronic means, aiming for greater efficiency and reduced administrative burden (CMS.gov). Starting January 1, 2027, certain health plans regulated by CMS are mandated to implement and maintain Prior Authorization APIs to facilitate this electronic exchange.
- Durable Medical Equipment, Prosthetics, Orthotics, and Supplies (DMEPOS) - A specific prior authorization process exists for certain DMEPOS items to address questionable billing practices and improper payments (CMS.gov). The Required Prior Authorization List for DMEPOS items identifies those frequently subject to unnecessary utilization based on criteria such as average costs and reports from oversight bodies.
- Third-Party Liability - State health care authorities, such as the Washington State Health Care Authority, operate under requirements to ascertain the legal liability of third parties, including health insurers and managed care organizations (Social Security Act of 1902(a)(25)). This ensures that other funding sources are billed before public programs like the Department of Social and Health Services (DSHS) act as the payer of last resort.
Government Cloud Services Authorization
For cloud products and services utilized by federal agencies, a specialized authorization framework known as FedRAMP (Federal Risk and Authorization Management Program) is in place. This program provides a standardized approach to security assessment and authorization, ensuring that cloud solutions meet stringent government security requirements.
- Standardized Security Approach - FedRAMP establishes a uniform method for security and risk assessment across all federal agencies, which helps in fostering confidence in cloud solutions (GSA.gov).
- FedRAMP Board - A dedicated board, composed of federal technology executives from various agencies, represents the interests of the federal community and the program as a whole (GSA.gov). This board plays a crucial role in guiding the authorization process and ensuring its effectiveness.
- Authorization Process - Cloud Service Providers (CSPs) must undergo a rigorous assessment process to achieve a FedRAMP authorization, demonstrating compliance with security controls. This authorization then allows federal agencies to confidently adopt these cloud services.
Workers' Compensation Programs
Within the Office of Workers' Compensation Programs (OWCP), authorization subsystems are critical for managing medical treatment and services for injured workers. These systems ensure that requested services are related to the accepted claim and are medically appropriate.
- Authorization Subsystem - The OWCP utilizes an authorization subsystem to process and review authorization requests for medical treatments and services (OWCPMed.DOL.gov). This system is designed to verify the validity of requests and assign unique identification numbers.
- Submission Methods - Providers can submit authorization requests through various channels, including paper templates, Direct Data Entry (DDE) via the Provider Portal, or through interfaces for specific programs like DEEOIC Home Health Authorization and DCMWC Diary Action Code (DAC) Authorization (OWCPMed.DOL.gov).
- Verification Process - Each authorization request undergoes a verification process within the WCMBP System to ensure it contains all necessary and valid information before approval or further review (OWCPMed.DOL.gov).
Key Components and Verification

Regardless of the specific application, authorization lists and the systems that manage them share common operational principles and verification methods to ensure accuracy and compliance. These components are essential for the integrity of the authorization process.
- Unique Identification Numbers - Every authorization request, once submitted and verified, is typically assigned a unique identification number (OWCPMed.DOL.gov). This allows for easy tracking, referencing, and auditing of specific approvals.
- Data Verification - Authorization systems are designed to verify that all submitted requests contain valid information (OWCPMed.DOL.gov). This often involves cross-referencing against existing records, policy rules, and eligibility criteria.
- Required Prior Authorization List - For specific items or services, such as certain DMEPOS items under Medicare, a defined list dictates which items always require prior authorization (CMS.gov). This list is based on data analysis and reports indicating potential for unnecessary utilization.
- Payer of Last Resort Considerations - In public health programs, mechanisms are in place to ensure that other liable parties (e.g., private insurers) are billed first before public funds are utilized (HCA.WA.gov). This principle is often supported by legal frameworks such as the Social Security Act of 1902(a)(25).
Benefits of Authorization Systems
Implementing robust authorization systems and maintaining comprehensive authorization lists offers several significant benefits across various sectors. These advantages contribute to greater efficiency, financial prudence, and enhanced compliance.
- Prevention of Improper Payments - By requiring pre-approval for certain services or items, authorization processes significantly reduce the incidence of fraudulent or erroneous billing (CMS.gov).
- Improved Resource Allocation - Authorization ensures that resources, whether financial or service-related, are directed only to those who genuinely qualify and for services that are deemed necessary.
- Enhanced Compliance - These systems help organizations adhere to complex federal and state regulations, minimizing legal and financial risks associated with non-compliance.
- Streamlined Operations - Especially with the advent of electronic authorization processes, administrative burdens can be reduced, leading to faster approvals and more efficient service delivery (CMS.gov).
- Data-Driven Decision Making - The data collected through authorization requests can provide valuable insights into utilization patterns, helping policymakers and program administrators identify areas for improvement or potential vulnerabilities.
Frequently Asked Questions
Sources
- Electronic Prior Authorization | CMS - Provides information on the electronic prior authorization process for medical items and services, including goals and benefits.
- Authorization Overview | Office of Workers' Compensation Programs - Describes the authorization subsystem for processing and reviewing authorization requests, including submission methods and verification processes.
- FedRAMP | GSA - Provides a standardized approach to security and risk assessment for cloud products and services, including the FedRAMP authorization process.
- Prior Authorization Process for Certain Durable Medical Equipment, Prosthetics, Orthotics, and Supplies (DMEPOS) Items | CMS - Details the prior authorization process for certain DMEPOS items, including the Required Prior Authorization List and operational guides.
- Viewing Authorization List | Washington State Health Care Authority - Provides guidance on viewing the Authorization List, including payer responsibilities and third-party liability considerations.
Not the form you're looking for?
Try our legal document generator to create a custom document
Ask about an Authorization List
Example questions:
Disclaimer: The templates available on this website are provided for general informational purposes only and do not constitute legal advice. They are not intended to be, and should not be interpreted as, compliant with any specific legal, regulatory, or privacy requirements. These templates are not a replacement for professional legal guidance and should not be relied upon for any particular matter or circumstance. Users are strongly encouraged to seek advice from a qualified attorney licensed in their jurisdiction before using, modifying, or relying on any template.
All templates are provided on an "as is," "with all faults," and "as available" basis. The provider disclaims any and all warranties of any kind, whether express, implied, statutory, or otherwise, including without limitation warranties of merchantability, fitness for a particular purpose, title, or non-infringement.
LegalTemplates.com makes no guarantees or representations regarding the accuracy, completeness, expected outcomes, or reliability of the materials contained in these templates or any materials referenced or linked from them.